ASR Rules Defender Recommendations
In the Microsoft 365 Defender Recommendations, there are some security controls about Attack Surface Reduction (ASR). It is highly recommended to implement these security measures, which can be seen in the Impact Score. You must also set ASR Rules for Azure VM’s.
Table of Contents

But what exactly are ASR rules and how do they work?
One of the best articles about it can be found here: Create & Audit an ASR Policy (Argon Systems)
The article was published some time ago but is still a very good knowledge base for it. It also describes how to distribute the settings to devices via MDM (Microsoft Intune). Be sure to check it out and understand what the ASR Rules are all about.
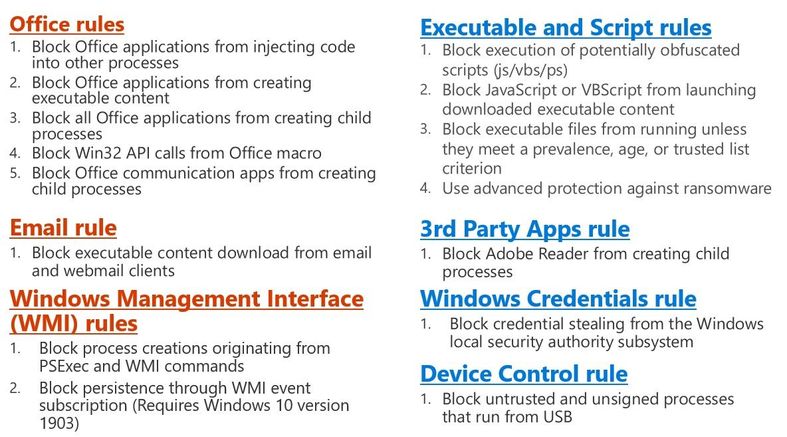
Here is a good summary of the ASR rules divided into categories.
Configure with “ASR Rules PoSh GUI”
Attack Surface Reduction Rules can be set on different ways. If you don’t use any Device Management and no Group Policies, there’s only one way left: Powershell. On the other hand, if all devices are configured via Intune Device Configuration Profile, but there are still the Azure VM remaining which are not managed via MDM or Group Policies.
For exactly these application purposes we can use the ASR Rules PoSh GUI tool. It is easier than doing all configurations via PowerShell. (especially the GUID)
https://github.com/hemaurer/MDATP_PoSh_Scripts
Prerequisites
- You can set attack surface reduction rules for devices that are running any of the following editions and versions of Windows:
- Windows 10 Pro, version 1709 or later
- Windows 10 Enterprise, version 1709 or later
- Windows Server, version 1803 (Semi-Annual Channel) or later
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012 R2
- Windows Server 2022
- The Powershell Script as well as the Exe have to run in admin mode to work properly.

There is no installation as the EXE is based on the Powershell Script. Learn more about the specific ASR Rules in the Microsoft Docs. Learn more about Intune Troubleshooting in my Blog Archive.
Conclusion
That the ASR rules are set is a must. The end-user device can certainly be configured via MDM or Group Policies, which definitely makes sense.
But maybe there are still Azure VM’s which are not in a domain or also do not get policies via MDM. Exactly for such systems there are simple ways to have increased security as well and to blow the Microsoft Secure Score through the roof.
